AngryFuzzer - Another fuzzing tool
AngryFuzzer is an accumulation of devices for pen-testing to assemble data and find vulnerabilities of the objectives dependent on Fuzzedb https://github.com/fuzzdb-venture/fuzzdb venture. It discovers shrouded documents and registries on a web server. The application attempts to discover URL relative paths of the given site by comparing them with a given set.
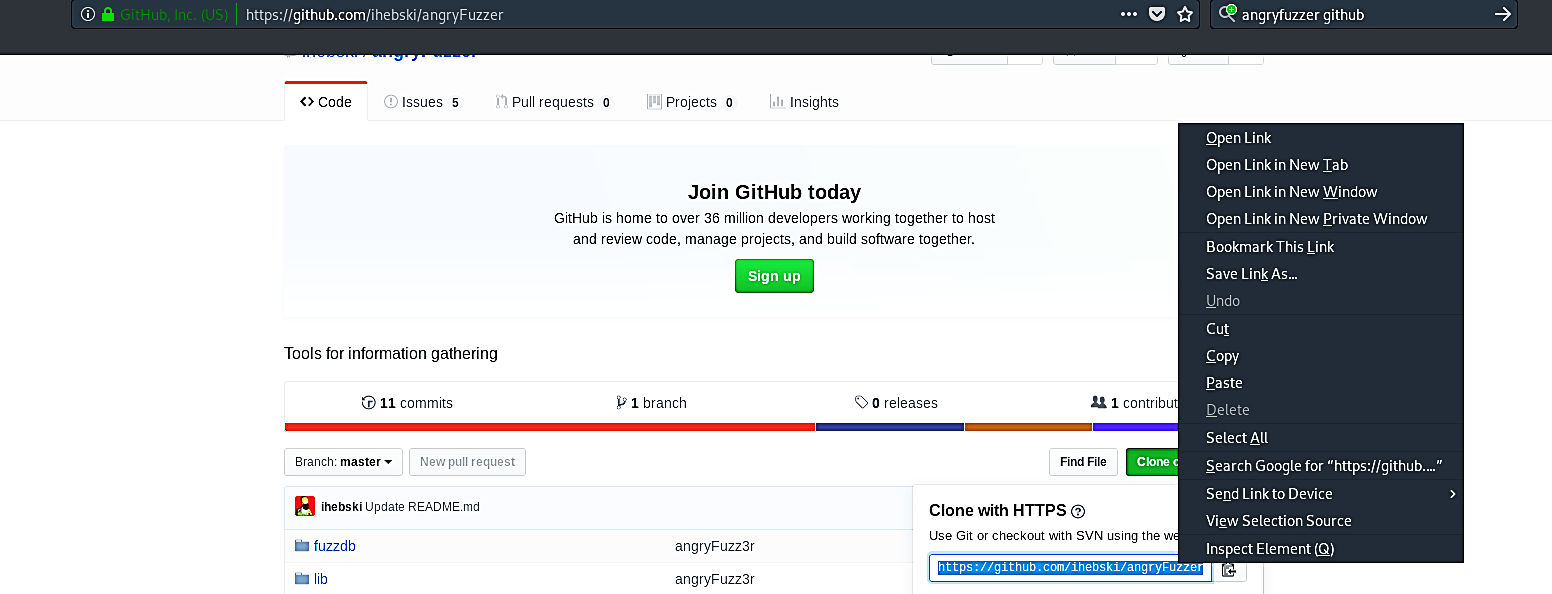
To download this tool, visit the following GitHub page “https://github.com/ihebski/angryFuzzer.”
Clone the tool into the “/opt” directory.
Ex: (root@kali:/opt# git clone https://github.com/ihebski/angryFuzzer.git).
Navigate to the “angryFuzzer” folder and install the required packages and libraries.
Ex: (root@kali:/opt/angryFuzzer# pip install -r requirements.txt).
To start the fuzzer, use the “python” command.
Ex: (root@kali:/opt/angryFuzzer# python angryFuzzer.py –h).

Let’s perform a default fuzzing attempt on a specific website and see what we can gather.
Ex: (root@kali:/opt/angryFuzzer# python angryFuzzer.py –u https://www.exampledomain.com/).

The screenshot shows that the tool successfully retrieved multiple URL relative paths that might be vulnerable and give out some sensitive information.
