“Defend the Web” write-up (World of Peacecraft)
“Defend the Web” write-up (World of Peacecraft / Realistic — dumpster diving for emails)
Hackers regard your email inbox as a treasure chest. As a result, your inbox is a treasure mine of personal information. Consider the data that could be obtained: you have emails related to your online banking information, federal taxes, medical bills, and internet shopping. By selling all of this information on illegal sites, hackers may make a fortune. That is why you must have unbreakable security measures in place. One typical blunder makes it easier for hackers to gain access to this Pandora’s box of personal information.
This particular challenge is very easy because it provides you access to the target’s account already. The target is addicted to World of Peacecraft and it will really screw him over if you could get access to his account.
You have got access to a target’s email account: let’s take a look at it.
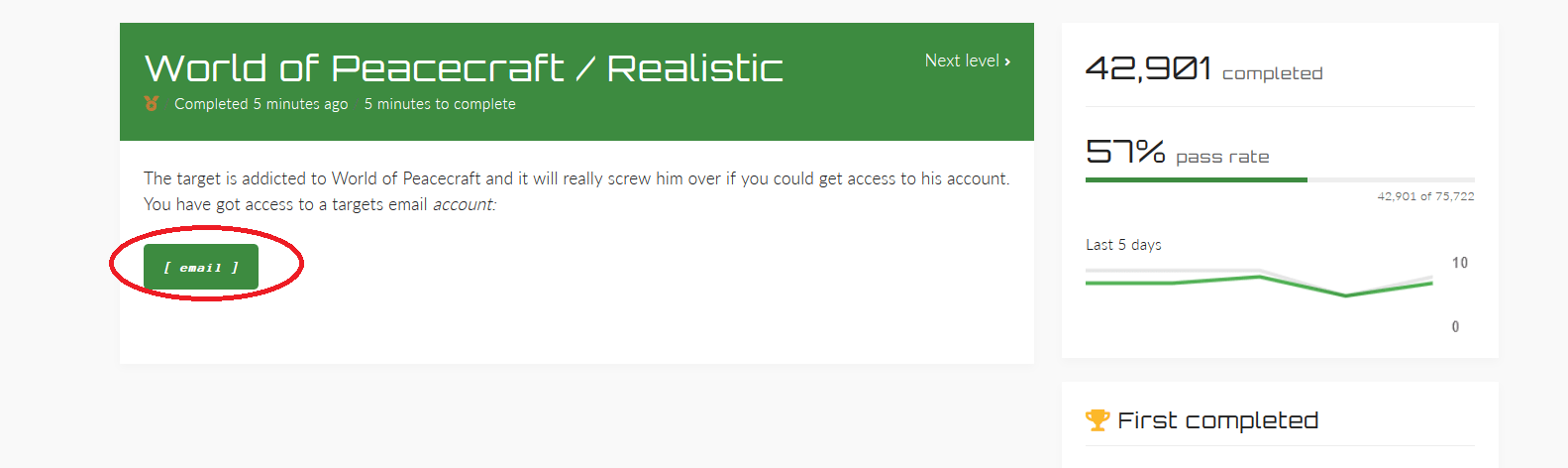
Supposedly somehow we hacked into the victim’s email, from this point we should do an in-depth search to find some good stuff. Click on the “email” button to view the victim’s email account.

We can see that he already received an activation link for his game. When you click on the link, it should take you to the page asking to submit the activation code. So, we should look further maybe in the “Trash” folder or any other folders, and try to find a code.

Looks like we found it. Click on the link to view the passcode.
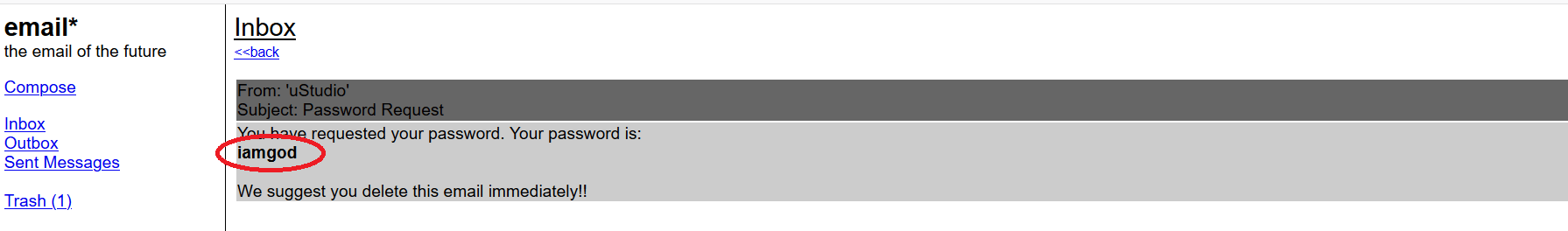
Copy the code and go back to the “Inbox” folder, then click on the “Activate account” link.

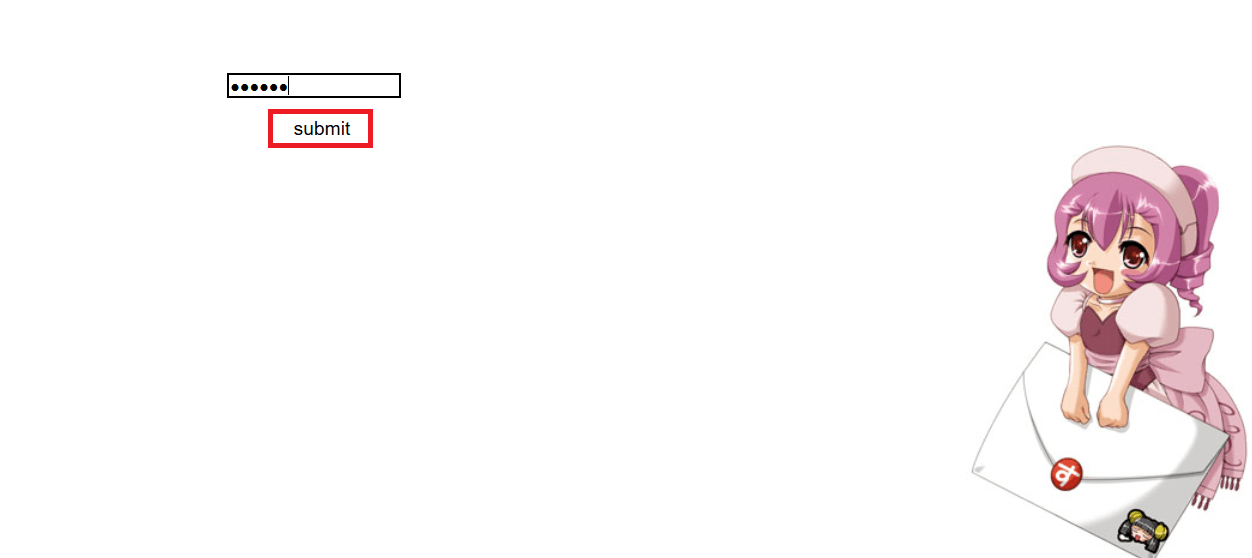
Click on the URL and paste the passcode to pass the challenge.

Because each email application is different, talking about a secure email deletion process is more complex. However, the majority of them are computer-like. When you send an email to the trash, it is almost certainly not removed. Some email programs remove discarded emails after a set period of time, while others preserve them until you run out of space. Most offer a ‘delete forever’ option that allows you to choose which emails in your trash folder you want to remove permanently. If you’re concerned about email recovery, some email systems, such as Outlook, provide a setting that allows you to turn off any email recovery. Remember that the sender may still have a copy of the email, or you may still have a copy in your sent folder.
For more information on email security best practices, we suggest you read the following article from “Email Analytics”.
