Information gathering using Discover
When conducting a penetration test, it’s critical to take a systematic approach to data collection and divide the activity into two parts: passive data collection and active data collection. Gathering passive data should come first. It entails gathering publicly available information about the organization being evaluated from the internet without communicating with the target systems.
Passive information collecting is scouring the internet for publicly available information about the firm that can be used to exploit its systems and circumvent security safeguards while conducting the pentest. Passive information collection can be done in a variety of ways, including manually surfing public internet sites, querying DNS, or using open-source intelligence (OSINT) gathering technologies to automate information discovery. The majority of these approaches aren’t technically advanced, but they do represent a hacker’s mindset, therefore you’ll want to use similar tactics when conducting your pentest.
One of the tools that can be used for this purpose is called “Discover”. Discover is a disclosure framework for quickly and accurately identifying underlying data about an organization or system. This tool mechanizes many hunts in a single device. For example, it can search for people within that organization or domain on all of the standard social media sites (such as LinkedIn), use traditional domain tools (such as goofile, goog-mail, theHarvester, search email collector, and mydnstools), and connect to other 3rd party devices to conduct additional searches.
To download this tool, go to the following website “https://github.com/leebaird/discover“ and copy the downloadable link.

Navigate to the “/opt” directory and use the “git clone” command to download the tool.
Ex: (root@kali:/opt# git clone https://github.com/leebaird/discover.git).
Change your directory to “/discover” and run the tool.
Ex: (root@kali:/opt/discover# ./discover.sh).

Let’s gather some information about a person. Select option “2” and provide the full name of a person you want to investigate then hit “Enter.”

Once you hit “Enter,” the Discover tool will open up multiple tabs of various people’s search platforms and try to find all possible information regarding your target.

Now, let’s perform a passive recon of a particular web server. Select the option “1” and hit “Enter.”

Provide the company name, and the target domain then hit “Enter.” For this demonstration, we will be targeting our virtual machine that runs the vulnerable web server.

After the whole information gathering process is complete, the Discover tool will create a link to the supporting data folder.

Click on the link, and the whole folder with gathered information will be listed on the browser.
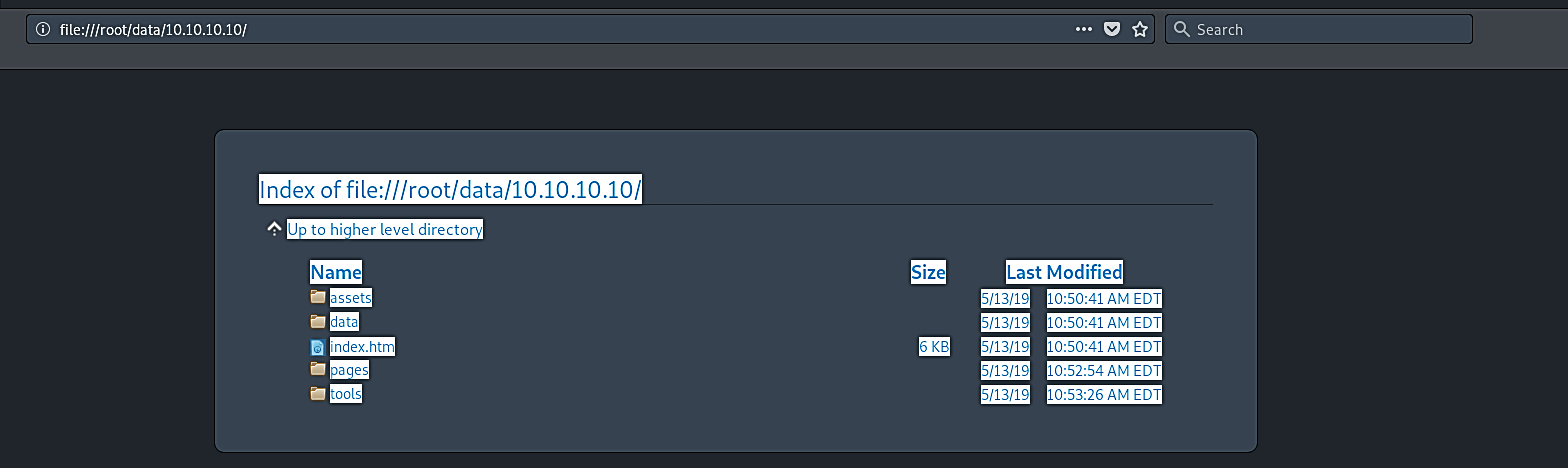
Each directory on the browser may contain some more information. Once you click on the hyperlinks, they will take you to a different page to show you what is inside so you can perform an in-depth investigation.

We can get a lot of information on the target, and it’s now up to us to filter out what’s relevant to the pentest. By default, everything must be maintained, and no information is useless; nonetheless, certain information is more interesting to a pentester than others. Services running on the host, software versions, employee names, and email addresses, IP addresses, hostnames, and architecture are just a few examples.
Everything that could be used by an attacker as an entry point is crucial information. The pentester can construct a threat map of the network or application now that we have adequate information about the target. He concentrates on the vector that he deems to be the easiest to employ and begins exploitation on that basis.
