Mass mailer attack using Social Engineering Toolkit
A mass mailer is generally used to send a phishing page link to the email ID of the objective. The aggressor should know about the email harvester technique to be proficient in this assault. A mass mailer is additionally used to play out a Distributed Denial of Service (DDoS) assault through the making of zombie bots and by controlling the bots through the control center.
Employees are typically unaware of the social engineering tricks and tactics that can be used to obtain sensitive information such as credit card information or corporate secrets. If an employee visits a malicious website, answers a social engineer’s phone call, or clicks on a malicious link sent to their personal or business e-mails, the entire organization’s security may be jeopardized.
In this post, we’ll show you how to submit a fake email using one of the most common tools, SET (Social Engineering Toolkit).
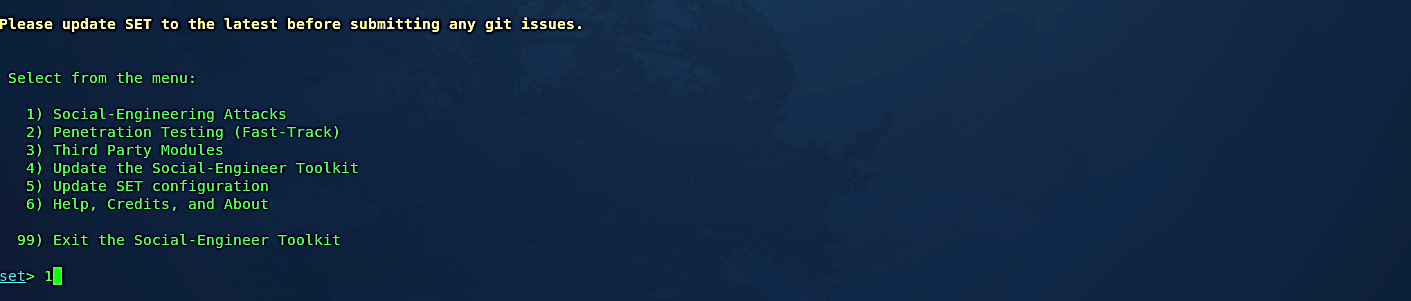
After starting “setoolkit” in your terminal, select option “1” for social engineering attacks and hit “Enter.”
To perform a mass-mailer attack, select option “5” then hit “Enter” to continue.

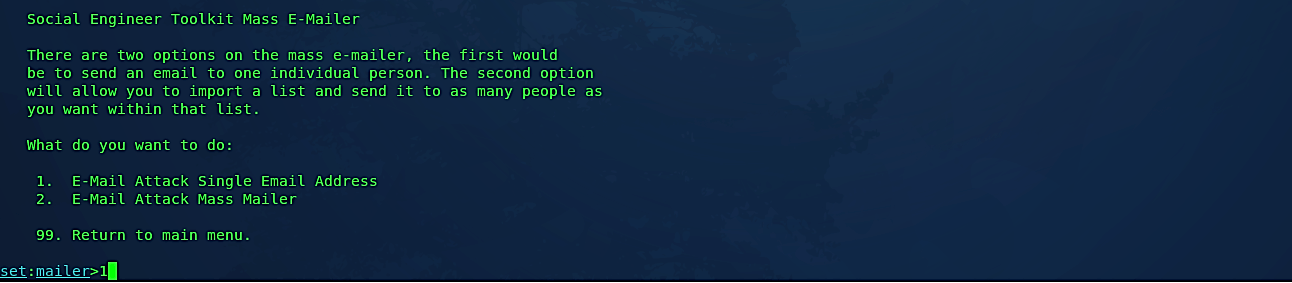
Then we need to select one of the two options available. In this example, we’ll be targeting a single person, so we chose the option “1.” However, if you want to send it to multiple targets, then select option “2.”
Next, specify the email address of the target person and select the option “1” to use a Gmail account for your attack.

Then provide the email address of the attacker and specify the “FROM NAME” option that the victim will see. Here we used a “FROM NAME” as “Bad Guy.”


Put the email subject and then type your message. Once you complete, type “END” to finish the process and press “Enter” to send the email.

As it is shown in the screenshot, our victim received an email from the Bad Guy.

This type of attack can be more effective if it is used with phishing attempts.

Organizations should perform ongoing employee security awareness training that, among other things, discourages users from publishing confidential personal or organizational information on social media to defend against this type of scam. In addition, businesses can invest in solutions that scan inbound emails for known malicious links or attachments. This solution should be able to detect signs of known malware as well as zero-day threats.
