Monitor any PC keyboard with SpyKey
By now, we all know that a keylogger is a sort of surveillance programming that once introduced on a framework, can record each keystroke made on that framework. Wouldn’t it be great if one specific tool can create a keylogger as well as a reverse shell that will assist you with getting access to the individual infected machine? So here, we will gain proficiency with a new tool called “SpyKey,” which can perform both this sort of errand (Keylogger and Reverse Shell), developed by “theLinuxchoice.”
SpyKey is FUD Win32 Keylogger and Reverse Shell, which work over the web with ngrok or server administration. You can download it from the following GitHub page: “https://github.com/thelinuxchoice/spykey.”

Copy the downloadable link and use the “git clone” command to download it to your computer.
Ex: (root@kali:/opt# git clone https://github.com/thelinuxchoice/spykey.git).

Once you downloaded the tool, navigate to the “spykey” directory run it using the “bash” command.
Ex: (root@kali:/opt/spykey# bash spykey.sh).

Next, choose a port number you want your payload run on, and provide a name for it. Here in this example, we selected the default port number and specified a name as “teamviewer” because we want our keylogger to look like a TeamViewer application.

Lastly, we need to select an appropriate icon for the keylogger. By default, SpyKey comes with two pre-installed icon archives, one for “messenger,” and another is for “Whatsapp.” If you want to use your icons, you need to download them and then specify the right location to it using the option “99”. For this purpose, we used the “http://www.iconarchive.com/“ webpage to download the “.ico” file for the TeamViewer application.

Select the option “99” and type a direct path to the icon location then hit “Enter.”

When the keylogger generation process is complete, it will save the file in the “spykey” directory and automatically start the listener to capture the incoming connections.
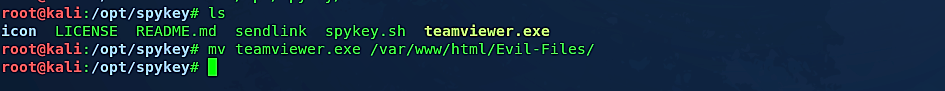
Using your social engineering skills, deliver this keylogger to the target computer. Once it ran the attacker computer will receive a reverse shell connection.

This keylogger monitors your keyboard and records every keystroke you make. When the software has gathered enough data, it sends it out in the form of an email.
Countermeasures
- If you suspect your device is being used by keyloggers, keep an eye out for unauthorized software and remove it.
- Downloading files from unknown sources is not a good idea.
- Use a virtual keyboard to enter password information on banking sites; in reality, use a virtual keyboard wherever possible.
- Use a password manager, which will automatically enter the password, eliminating the need for keystrokes.
- Use a strong and cutting-edge antivirus and internet protection suite that can protect your device from advanced and evolving cyberattacks while also detecting and removing malicious software.
