NetScanTools Pro
NetScanTools Pro is a coordinated accumulation of web data gathering and network troubleshooting utilities for Network Professionals. You can research IPv4 addresses, IPv6 addresses, hostnames, domain names, email locations, and URLs automatically or with manual tools. This tool is intended for the Windows operating framework and has a long client-driven improvement history. It is used by a considerable number of system experts and people associated with ethical hacking.
Download NetScanTools from the “https://www.netscantools.com/nstpromain.html” webpage, and install it on your computer. Once the installation is complete, let’s perform some scanning techniques using this tool.
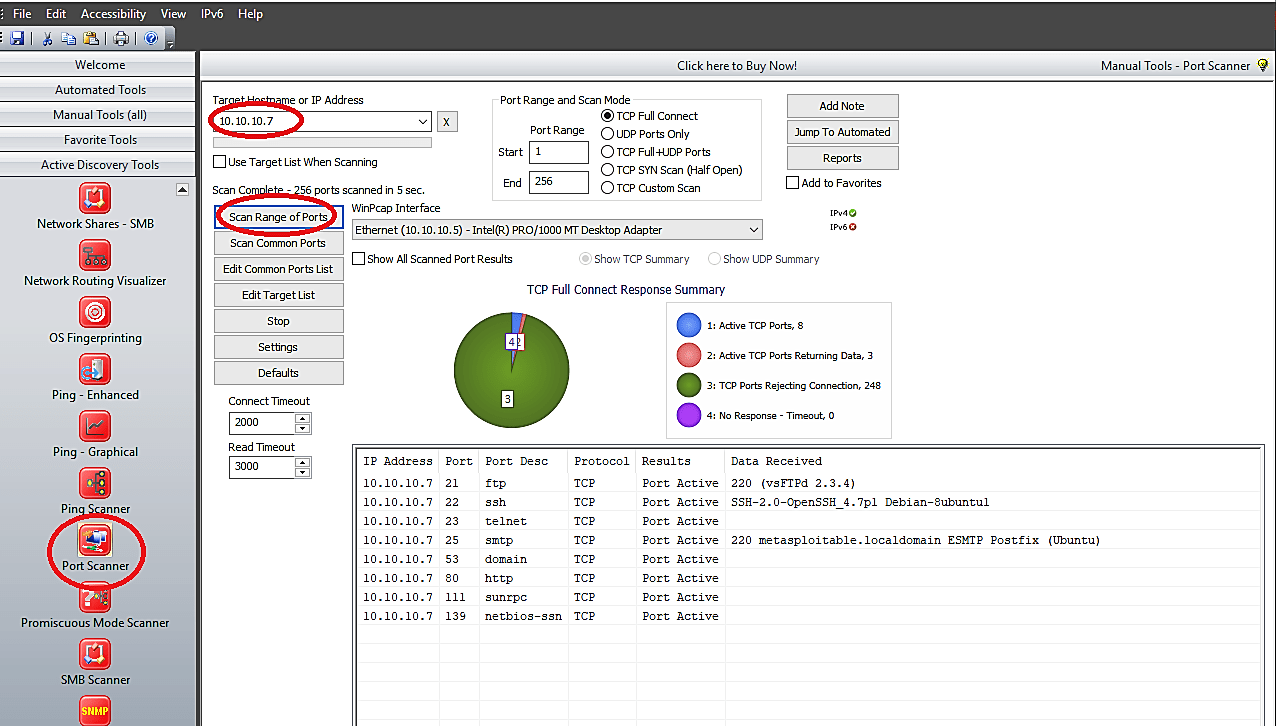
Port Scanner
Port Scanner is a fundamental security instrument for discovering open/ listening ports relating to the TCP or UDP services running on an objective gadget. This scanner enables you to run four unique types of examining patterns while searching for TCP or UDP open ports. You can scan a linear range of ports, a list of ports on one IP address, or a list of IP addresses.
You have full authority over connection timeouts, TCP packet headers, and other significant parameters. Any information received from the objective port upon association is saved for viewing. The outcomes are exhibited in the spreadsheet structure for a simple audit of results. An outline pie graph gives a snappy review of the responding and non-responding port data.
To use the “Port Scanner,” click on the “Active Discovery Tools” tab from the left pane and select the “Port Scanner” tool. Specify the target’s IP address, port range, scan mode, and then click on the “Scan Range of Ports” button to begin the process.
Ping Scanner
The Ping Scanner sends ICMP ping packets to each IP address in any scope of IPv4 addresses you determine. It searches for ICMP responses from dynamic gadgets. This instrument works over any range of IPv4 addresses, whether on your subnet or over the web. It can likewise ping a rundown of IPv4 addresses that you need to ping. Use Ping Scanner to find dynamic gadgets and accumulate other data about those PCs. Use this tool in conjunction with the Port Scanner for a full accounting of each IP address. This tool is also known as NetScanner or Ping Sweep.
To use the “Ping Scanner,” click on the “Active Discovery Tools” tab from the left pane and select the “Ping Scanner” tool. Specify the target’s IP address range and then click on the “Scan” button to begin scanning.

Traceroute
The Traceroute tool is an upgraded variant of the exemplary network troubleshooting instrument used to demonstrate the route packets take to an objective gadget over an IP network. The target gadget can be on a local area network or over the web. NetScan’s enhanced variant of traceroute supports the two Windows-style ICMP Echo Request and UNIX style UDP techniques. Progressed traceroute incorporates firewall penetrating TCP Traceroute, and UDP fixed port traceroute. All strategies rely upon returning ICMP packets from intermediate gadgets along the route.
To use traceroute, click on the “Active Discovery Tools” tab and select the “Traceroute-Graphical” tool. Provide the target’s IP address or hostname and then click on the “Run” button to begin the traceroute process.

ARP scan
The ARP scan uses ARP packets to find all active hosts in an IPv4 even if protected by a firewall created to hide the presence of the device. Since ARP is not routable, this type of scanner will only work on the local LAN.
To use this tool, click on the “Manual Tools (all)” tab and select the “ARP Scan (MAC Scan)” tool. Provide the IP range of your target network and click on the “Do Arp Scan” button.

