Perform various OSINT techniques with DataSploit
Regardless of whether you are assaulting an objective or protecting one, you need a clear picture of the dangerous scene before you get in. This is the place where DataSploit comes into play. Using different Open Source Intelligence (OSINT) apparatuses and strategies that they have observed to be powerful, DataSploit presents to them all into one spot, connects the crude information caught, and gives the client, all the applicable data about the location, email, telephone number, individual, and so forth. It enables you to gather valuable data about an objective that can grow your assault/safeguard surface all-around rapidly.
DataSploit was created with Python and essentially requires the absolute minimum information, (for example, area name, email ID, individual name, and so on.) before it goes out on a mining binge. The sources that are coordinated are all hand-picked and are known to give reliable data. We have utilized them beforehand during various offensive as well as defensive engagements and discovered them accommodating.
To download the tool, visit the GitHub page “https://github.com/DataSploit/datasploit“ and copy the downloadable link.

Navigate to the “/opt” directory and use the “git clone” command to download the tool.
Ex: (root@kali:/opt# git clone https://github.com/DataSploit/datasploit.git).
Next, give executable permission to all files in the “/datasploit” directory.
Ex: (root@kali:/opt# chmod -R 777 datasploit/).
Then we need to install all required packages using the “pip install” command to run this tool successfully.
Ex: (root@kali:/opt/datasploit# pip install -r requirements.txt).
Once DataSploit is installed successfully, you need to edit the “config.py” file to add your API keys. Run the below commands to open up the “config.py” file in a text editor.
Ex: (root@kali:/opt/datasploit# mv config_sample.py config.py)
Ex: (root@kali:/opt/datasploit# nano config.py)

If you need to create your API keys, visit the following “https://datasploit.readthedocs.io/en/latest/apiGeneration/“ web page, and it will present you with the instructions on how to get them.

To start the tool and view help/usage information, use the following command.
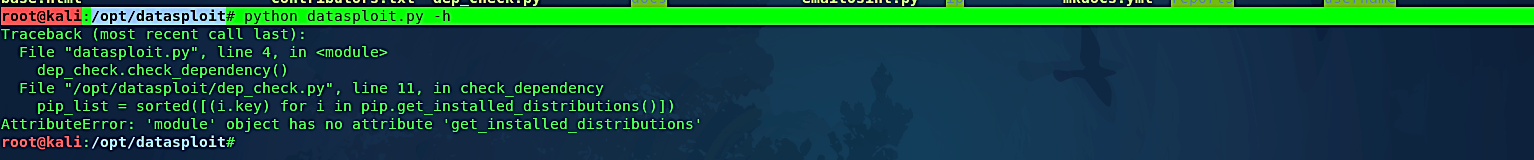
Ex: (root@kali:/opt/datasploit# python datasploit.py –h).
Note: During the startup process, you may encounter some errors like “get_installed_distributions.” To fix this problem, we need to do some configurations in the “dep_check.py” file.
Open up a “dep_check.py” file with any text editing tool and replace the red circled statements with the statements provided below.
Ex: (root@kali:/opt/datasploit# nano dep_check.py).

Remove the “import pip” statement and replace it with:
“ try:
from pip._internal.utils.misc import get_installed_distributions
except ImportError:
from pip import get_installed_distributions”
Remove the “pip_list = sorted([(i.key) for i in pip.get_installed_distributions()])” statement and replace it with:
“pip_list = sorted([(i.key) for i in get_installed_distributions()])”

Now we can run the same startup command, and it should work perfectly fine.

If you want to gather information regarding the particular website, use the following command: (root@kali:/opt/datasploit# python datasploit.py -i test.com).
To gather information regarding a specific email, use the following command: (root@kali:/opt/datasploit# python datasploit.py -i jdoe76781@gmail.com).
Note: when you run this command, you may face the error “No module named cfscrape.”

To fix this, install the module using the following command:
Ex: (root@kali:/opt/datasploit# pip install cfscrape).
