Shodan - the search engine for IoT
Today, a substantial number of devices are hooked up to the internet, ranging from cellphones and watches to air conditioners and refrigerators: this is known as the “Internet of Things,” or the network made up of physical items gathering and exchanging data. Of course, the improper setting of these devices might result in major privacy issues. Private webcams, or better yet, what they are supposed to be, are the simplest example: if they are set to have a public IP address and are not adequately secured, they can be accessed by anyone from anywhere in the world.
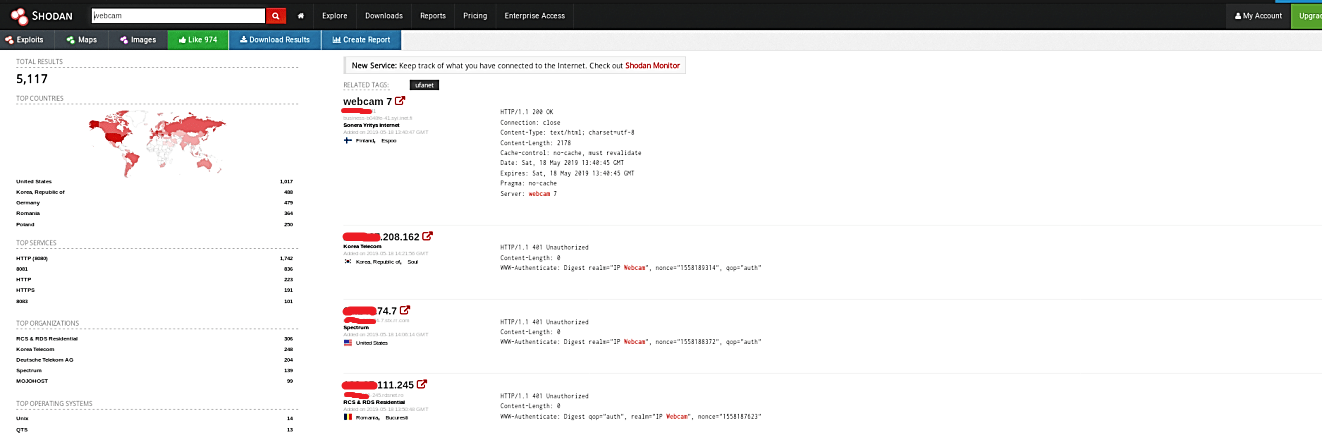
In contrast to Google, which creeps the Web searching for sites, Shodan explores the Internet’s back channels. It’s a sort of “dim” Google, searching for the servers, webcams, printers, switches, and the various stuff that is associated with and makes up the Internet.
Shodan runs every minute of every day and gathers data on around 500 million associated gadgets and administrations every month. Shodan searchers have discovered control frameworks for a water park, a gas station, an inn wine cooler, and a crematorium. Cybersecurity specialists have even found command and control frameworks for nuclear power plants and a particle-accelerating cyclotron by utilizing Shodan.
What’s exceptionally critical about Shodan’s capacity to discover the majority of this — and what makes Shodan so unnerving — is that not many of those gadgets have any security incorporated with them.
To start your Shodan search, visit the following link: “https://www.shodan.io/“ and type any domain name in the search field.

Shodan will get you many results related to the target website and list all available vulnerabilities, open ports, running services, and many more.

You can even search and view publicly available webcams around the globe and monitor the street city cameras.
You can also do a search based on the specific port numbers.


Experimenting with different types of filters can help you become more comfortable with queries and maximize the search engine’s potential. Shodan may be an extremely valuable tool for determining whether or not a company’s network contains crucial nodes that are either publicly exposed or improperly configured.
