Since January, the Android trojan has been present on the Google Play Store
- March 16, 2022

Cybersecurity experts monitoring the mobile app ecosystem have seen an increase in trojan infections on the Google Play Store, with one of the apps having over 500,000 installations and being available for download. The majority of these programs are part of a trojan software family that has been used in a variety of frauds, resulting in money losses as well as the theft of private information.
In addition, a new Android Trojan disguised as a WhatsApp mod has been discovered in the wild, spreading through malicious websites aided by social network posts, forums, and SEO poisoning. These findings were reported by Dr. Web in their review of virus activity on mobile devices in January 2022.
Crypto management apps, social assistance tools, Gasprom investment copies, photo editors, and a launcher themed after iOS 15 are among the risks detected in the Play Store by Dr. Web’s analysts.


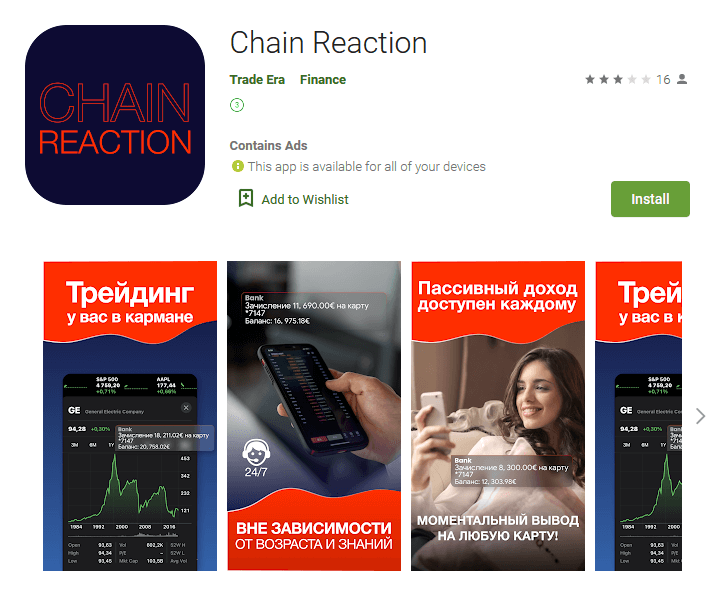
Most phony investing applications require victims to register a new account and deposit funds ostensibly for trading, but the funds are merely transferred to the scammer’s bank account. Other apps attempt to persuade users to sign up for costly memberships.
Most of the apps identified by Dr. Web have been withdrawn from the Play Store. Top Navigation, one of the identified apps that is still available on the Play Store, has over 500,000 installations, making this a big worry due to its broad use.

According to the research, apps discovered by Dr. Web would use Wap Click technology to load affiliate service sites and enable paid subscriptions after fooling the user into inputting their phone number.
The most major threat in January 2022, according to Dr. Web’s research, was trojanized versions of unapproved WhatsApp modifications like GBWhatsApp, OBWhatsApp, or WhatsApp Plus. Arabic language support, home screen widgets, a distinct bottom bar, conceal status choices, call blocking, and the ability to automatically save incoming media are all included in these mods. These mods are renowned in online forums because they add capabilities to WhatsApp that aren’t present in the standard version.

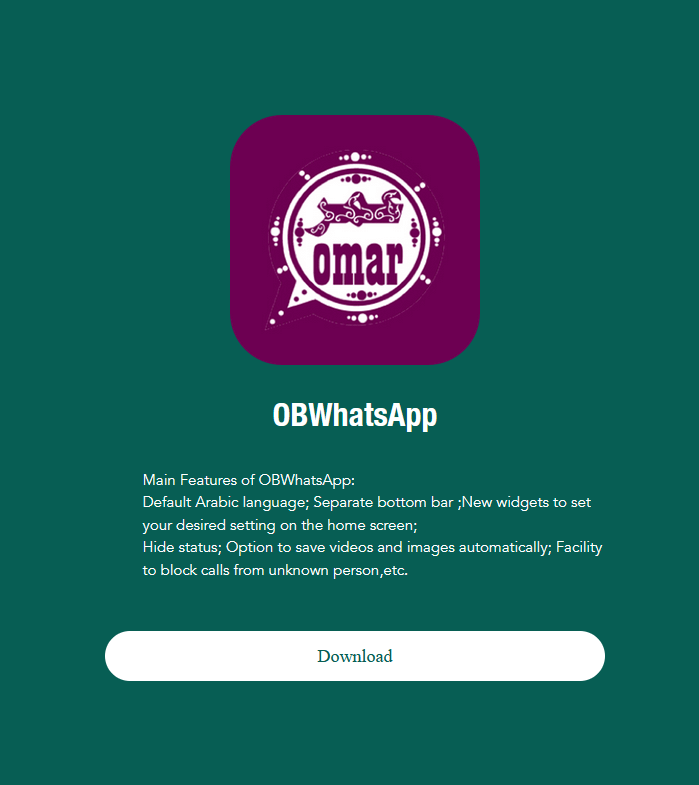
The trojanized versions, on the other hand, use the Flurry stat service to steal alerts from the Google Play Store and Samsung Galaxy Store apps. Furthermore, the trojan demands that the user install an additional APK from a URL obtained from the command and control server, posing as an update for OBWhatsApp. The attackers then utilize this new software to display dialog boxes at random, with text that is dynamically configured and changed remotely, allowing them to divert visitors to malicious websites.
Avoiding these programs requires preventing APK downloads from unknown sites, reading user reviews, examining permission requests before installation, and tracking battery and internet data usage afterward. Additionally, make sure to verify the status of Google Play Protect on a regular basis and add a second layer of security by using a trusted mobile security app.
