Thousands of GitLab instances are affected by a new security flaw.
- March 4, 2022

Security researchers have revealed details of a now-patched security flaw in GitLab, an open-source DevOps platform, that may enable a remote, unauthenticated adversary to retrieve user-related data. The medium-severity vulnerability, dubbed CVE-2021–4191 (CVSS score: 5.3), impacts all versions of GitLab Community Edition and Enterprise Edition starting with 13.0, as well as all versions starting with 14.4 and previous to 14.8.
Jake Baines, a senior security researcher at Rapid7, is credited with discovering and reporting the problem. Updates were issued as part of GitLab critical security releases 14.8.2, 14.7.4, and 14.6.5 on February 25, 2022, following a responsible disclosure on November 18, 2021.
In a report released Thursday, Baines stated, “The vulnerability is the result of a missing authentication check while executing specific GitLab GraphQL API queries.” “This vulnerability allows a remote, unauthenticated attacker to gather registered GitLab usernames, names, and email addresses.”
If the API information leak is successfully exploited, hostile actors may be able to enumerate and assemble lists of genuine usernames belonging to a target, which can then be used as a stepping stone for brute-force attacks such as password guessing, password spraying, and credential stuffing.
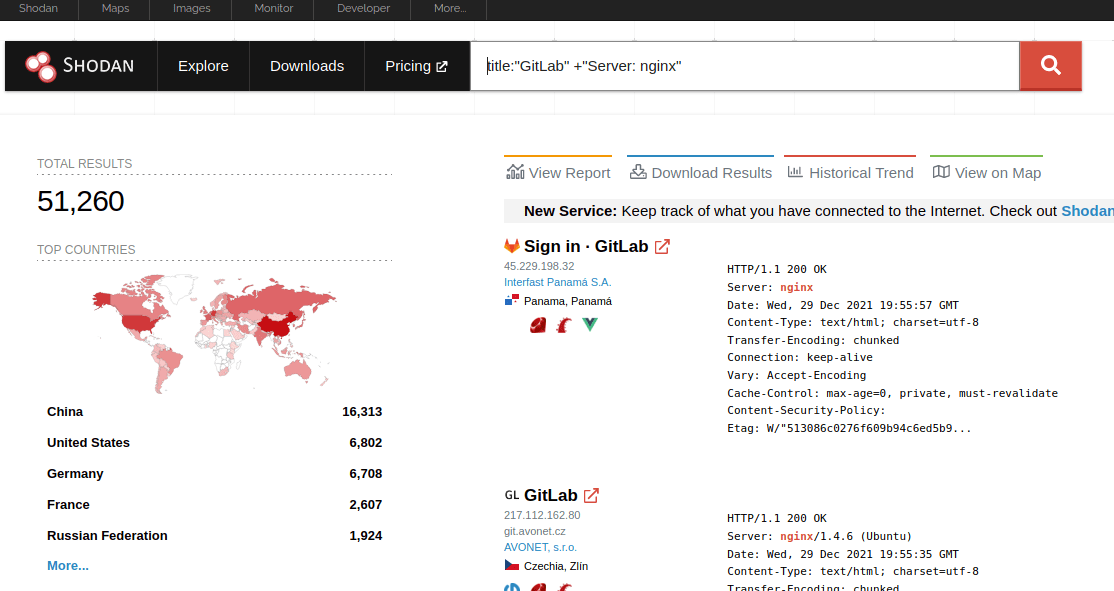
“The information leak might also allow an attacker to construct a new username wordlist based on GitLab installs — not only from gitlab.com but from the other 50,000 GitLab instances accessible through the internet,” Baines said.
The update also fixes six additional security weaknesses, one of which is a critical flaw (CVE-2022–0735, CVSS score: 9.6) that allows an unauthorized adversary to steal the runner registration tokens needed to authenticate and approve CI/CD tasks hosted on GitLab.
