Web Application Scanner - WAScan
WAScan is an open-source web application scanner that performs different penetration testing undertakings, including fingerprinting, assaulting, evaluating, brute force, and discovering sensitive information leaks. The fingerprinting tasks incorporate web structures, content administration framework, server, operating systems, languages, and web applications firewalls fingerprinting. The assaults performed by WAScan include SQL injections, blind SQL injection, bash command injection, HTML injection, PHP injection, LDAP injection, Xpath injection, XSS assaults, OS commanding, Local File Inclusion (LFI) checks, Server side infusion, and Buffer overflow assault.
WAScan can review Apache Status page, open redirect, PHPInfo, Cross-Site Tracing (XST), and Robots.txt records. The brute-force option can be utilized against administrator boards, backup directories, backup files, standard directories, shared files, and hidden parameters of the victim web application. Also, WAScan can search for sensitive data like credit card information, Social Security Number (SSN), private IPs, messages, and fatal errors.
You can clone the most recent variant of the instrument from the GitHub source, using the following link: “https://github.com/m4ll0k/WAScan.”
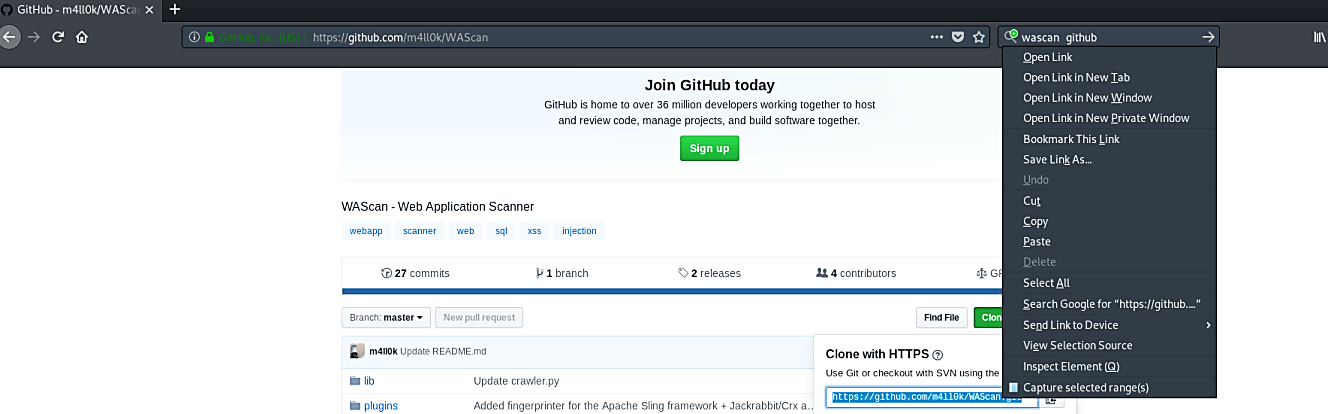
Clone the tool (root@kali:/opt# git clone https://github.com/m4ll0k/WAScan.git) and run it with the “python” command (root@kali:/opt/WAScan# python wascan.py). It will display the help page and usage information.

To perform basic web application vulnerability scanning, after running the tool, specify the target URL.
Ex: (root@kali:/opt/WAScan# python wascan.py – -url http://10.10.10.10).
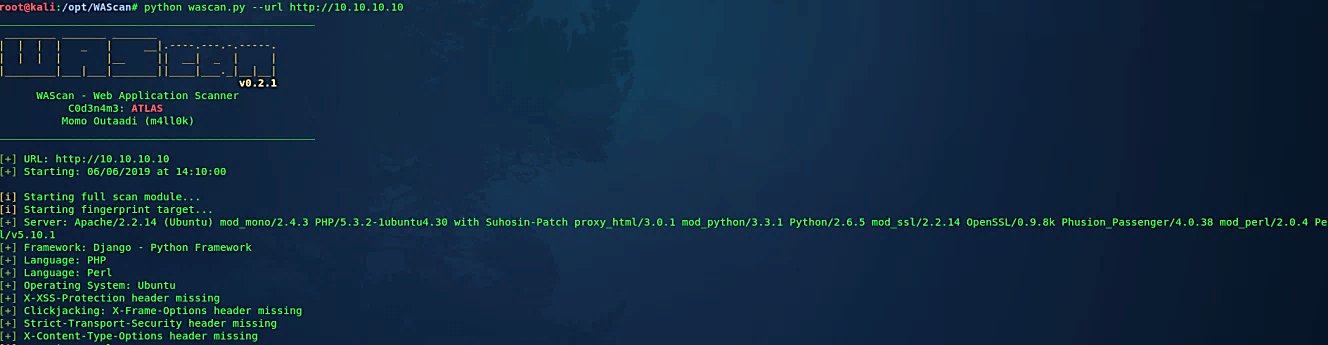
In the attack mode, the WAScan tool dispatches the assault modules to test if the target web application is vulnerable against any of the previously mentioned attacks. Any conceivable attack will appear in the outcomes alongside the vulnerable paths, as appeared in the accompanying screenshot.
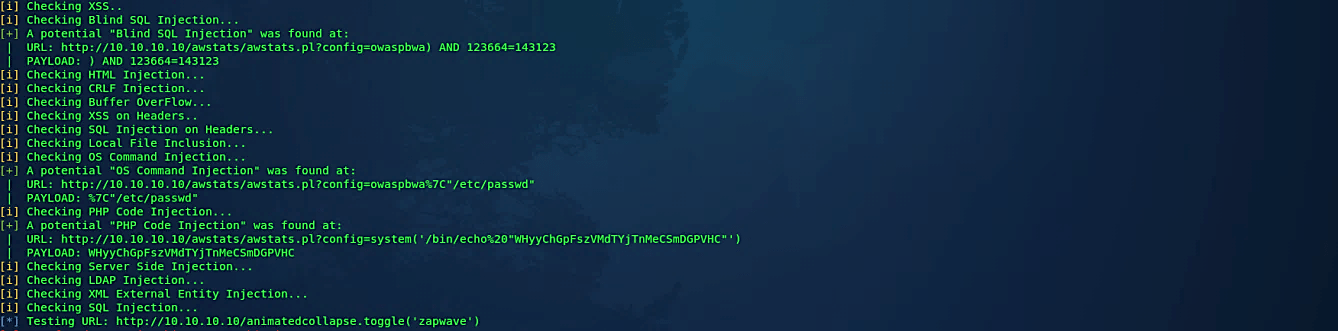
This semi-automated web application tool can be used to collect information and attack web applications. The tool can detect vulnerabilities in web applications that can lead to SQL injections, cross-site scripting, OS commanding, and server-side injections, among other cyber-attacks.
